Trivy Security has suffered a significant compromise affecting at least one customer. Based on evidence from our SOC, the blast radius is likely to expand.
trivy-action and setup-trivy.aquasecurity/trivy-action, causing tag-pinned workflows to execute malicious code..env files, and in-memory secrets from GitHub Actions runners.scan.aquasecurtiy[.]org, with fallback via a public GitHub repository in the victim account.This incident was not a single failure — it reflects weak supply-chain discipline.
Unbounded trust in third-party execution
External CI/CD components were treated as safe dependencies instead of remote code execution inside privileged environments.
Weak supply-chain governance
Mutable dependencies, incomplete containment, and poor version control enabled persistence and escalation.
These are systemic issues that repeatedly lead to large-scale compromise and should be flagged in any serious technical due diligence. We actively look for these issues within our deep analysis services such as during Architectural Review or Technical Due Diligence.
| What’s happening | Evidence | Risk | What to do |
|---|---|---|---|
| External CI/CD components acted as a direct execution path into trusted environments | Malicious code in Trivy CI/CD repos executed before scans (Socket); nearly all trivy-action tags redirected to attacker commits (Wiz, Socket) |
Pipelines run attacker-controlled code with access to credentials, tokens, and deployment systems; tag pinning fails if upstream is mutable | Remove third-party CI/CD dependencies where possible; move pipeline logic in-house; if required, mirror internally, pin to immutable commits, and gate updates |
| Attackers reused credentials due to incomplete containment | Aqua confirmed reuse of credentials from March 2026 breach | Partial remediation leaves persistent access to source control and release systems | Perform atomic credential rotation across all systems; invalidate sessions; remove unnecessary access; verify no dependency on compromised credentials |
| Tag-based workflows silently inherited malicious code | 75 of 76 tags were force-pushed to malicious commits | Mutable references allow silent, large-scale compromise | Monitor for force-push and drift; require immutable pinning; control dependency updates |
| Malware targeted CI/CD runners and developer machines for credential harvesting and persistence | Broad credential harvesting across cloud and tooling; memory scraping of GitHub Actions runners; persistence via systemd user services | A single dependency compromise can expose entire environments and enable long-term access | Treat affected systems as fully compromised; hunt for persistence; rotate all reachable credentials |
| Exfiltration used typosquatted domains and GitHub fallback | Data sent to scan.aquasecurtiy[.]org; fallback via public repo creation |
Data theft blends into normal traffic and bypasses traditional controls | Monitor egress to suspicious domains; alert on unexpected GitHub activity and repo creation from CI/CD identities |
| Supply-chain compromise expanded via automated propagation (npm worm) | CanisterWorm republished malicious packages across 28 packages in under 60 seconds (Aikido) | Rapid cascading compromise across package ecosystems | Restrict and rotate publish tokens; enforce stronger release controls; monitor for anomalous publishing activity |

SkySiege’s Cloud Assessment is a custom-built, automated Cloud Platform Assessment that scans your AWS resources and infrastructure to identify security and architecture concerns. All results are compiled to a PDF report that details what the issues are, why they’re an issue, which resources are involved and how to fix them.
We provide assessments in two formats:
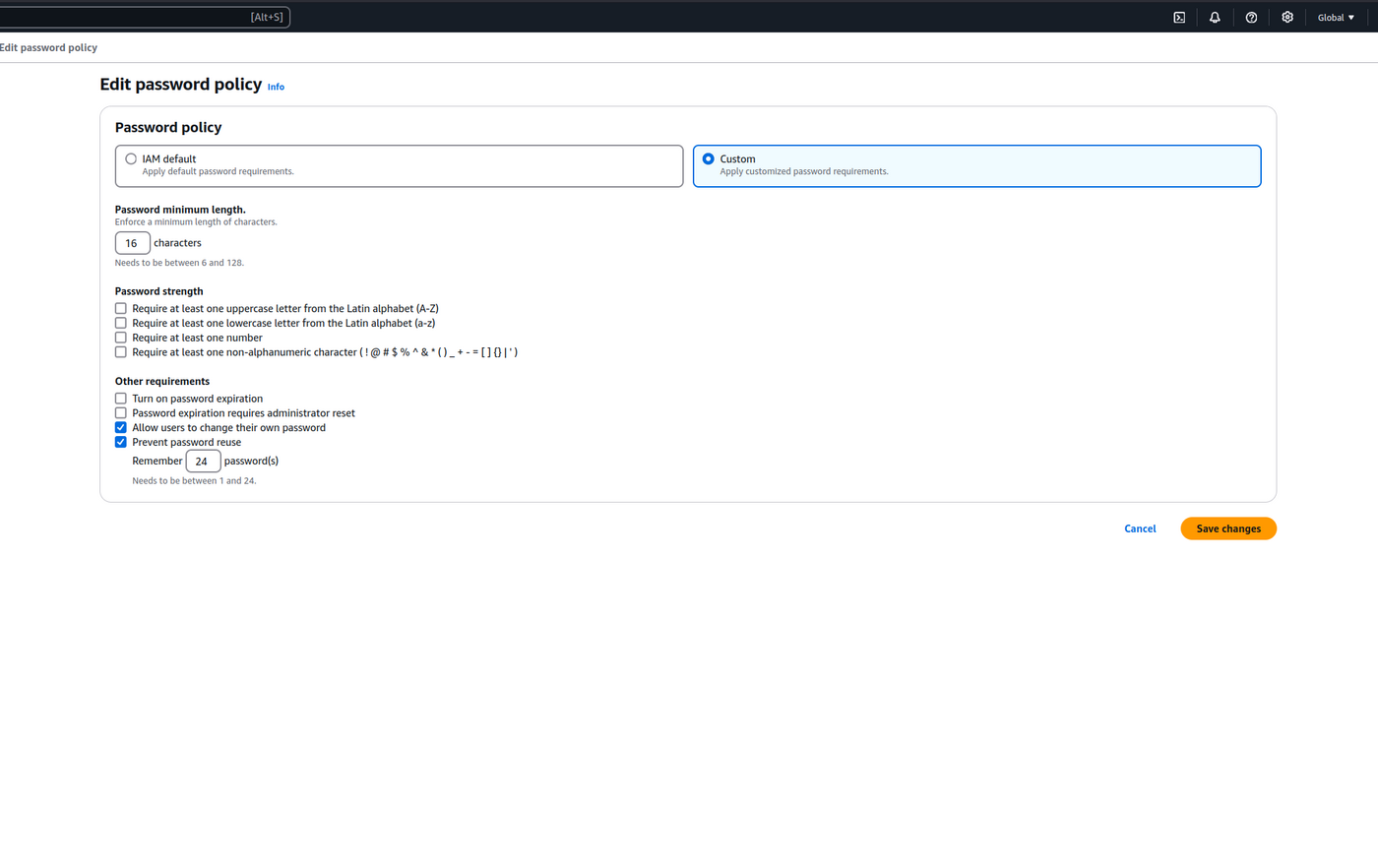
The AWS Password Policy dictates the security standards and management of AWS IAM User passwords used for access to the AWS Console. We extend the default policy to increase security and minimise additional processes providing the most efficient password management configuration we can design.
cspm cloud guidance