BleepingComputer reports that Aura confirmed unauthorised access to nearly 900,000 records after a voice phishing attack against an employee. Aura says the exposed dataset came from a marketing tool inherited through a 2021 acquisition and that only about 35,000 records related to current or former Aura customers. The rest were legacy marketing contacts carried forward from the acquired company. Have I Been Pwned found the leaked data also included customer service comments and IP addresses, while ShinyHunters claimed to have stolen 12GB of customer and corporate data.
The key lesson is not just phishing exposure. This incident shows how retained legacy data from M&A activity can become a long-lived liability, especially when old marketing datasets remain accessible years after acquisition. The product team should treat inherited systems, SaaS tools and contact databases as high-risk assets that require explicit retention review, access control validation and decommissioning decisions. BleepingComputer’s reporting and Aura’s disclosures point to a preventable risk: data that may no longer be operationally necessary was still present and reachable when the compromise occurred.
| What’s happening | Cause | Action |
|---|---|---|
| Legacy acquisition data became breach material Nearly 900,000 exposed records came from a marketing database inherited in an acquisition, not primarily from Aura’s active customer base. Old contact data remained available years later and was ultimately exposed. |
Retained acquired data was not fully eliminated, isolated, or reduced after integration. | Check for inherited databases, marketing tools and SaaS datasets from acquisitions; specifically flag large legacy contact stores that remain active years later without clear business need or retention justification. |
| A phishing-resistant control failed at the user access layer Aura says a voice phishing attack against an employee led to unauthorised access. This indicates an attacker could socially engineer access to a system holding sensitive data. |
Employee-targeted authentication and helpdesk-style verification controls were insufficient against vishing. | Check whether access to SaaS platforms and inherited systems is protected by phishing-resistant MFA, conditional access and strong identity verification for account recovery or support workflows. |
| Sensitive but non-core data was still valuable to attackers The exposed records included names, emails, home addresses, phone numbers and, per Have I Been Pwned, customer service comments and IP addresses. Even without SSNs or financial data, the dataset was still worth extorting and leaking. |
Data minimization and field-level exposure reduction were not strong enough for lower-priority business systems. | Check what PII and metadata are stored in marketing and service platforms; specifically identify unnecessary address, phone, comment and IP retention in non-production or non-core systems. |
| Post-acquisition visibility appears incomplete Aura distinguished between 35,000 customer records and roughly 900,000 inherited records, showing the breached data estate extended beyond the company’s primary customer population. This suggests the acquired data footprint had ongoing exposure significance. |
M&A integration did not fully normalise inventory, ownership and security review of inherited data sources. | Check whether acquired applications and datasets are fully represented in asset inventory, ownership records and security reviews; specifically identify systems inherited through transactions that still hold personal data. |
This breach creates direct legal, reputational and operational risk because a large volume of personal data was exposed from a legacy dataset that may not have been necessary to retain. BleepingComputer’s reporting shows the main affected population was not Aura’s active customers but a much larger inherited marketing list, which increases scrutiny around retention governance and post-acquisition controls. For buyers, investors and security teams, this is a detection and visibility problem: if inherited SaaS tools and dormant datasets are not tracked, reviewed and retired, they become hidden breach material. That drives notification costs, regulatory exposure, incident response spend and brand damage while showing weak control over the acquired data estate.

SkySiege’s Cloud Assessment is a custom-built, automated Cloud Platform Assessment that scans your AWS resources and infrastructure to identify security and architecture concerns. All results are compiled to a PDF report that details what the issues are, why they’re an issue, which resources are involved and how to fix them.
We provide assessments in two formats:
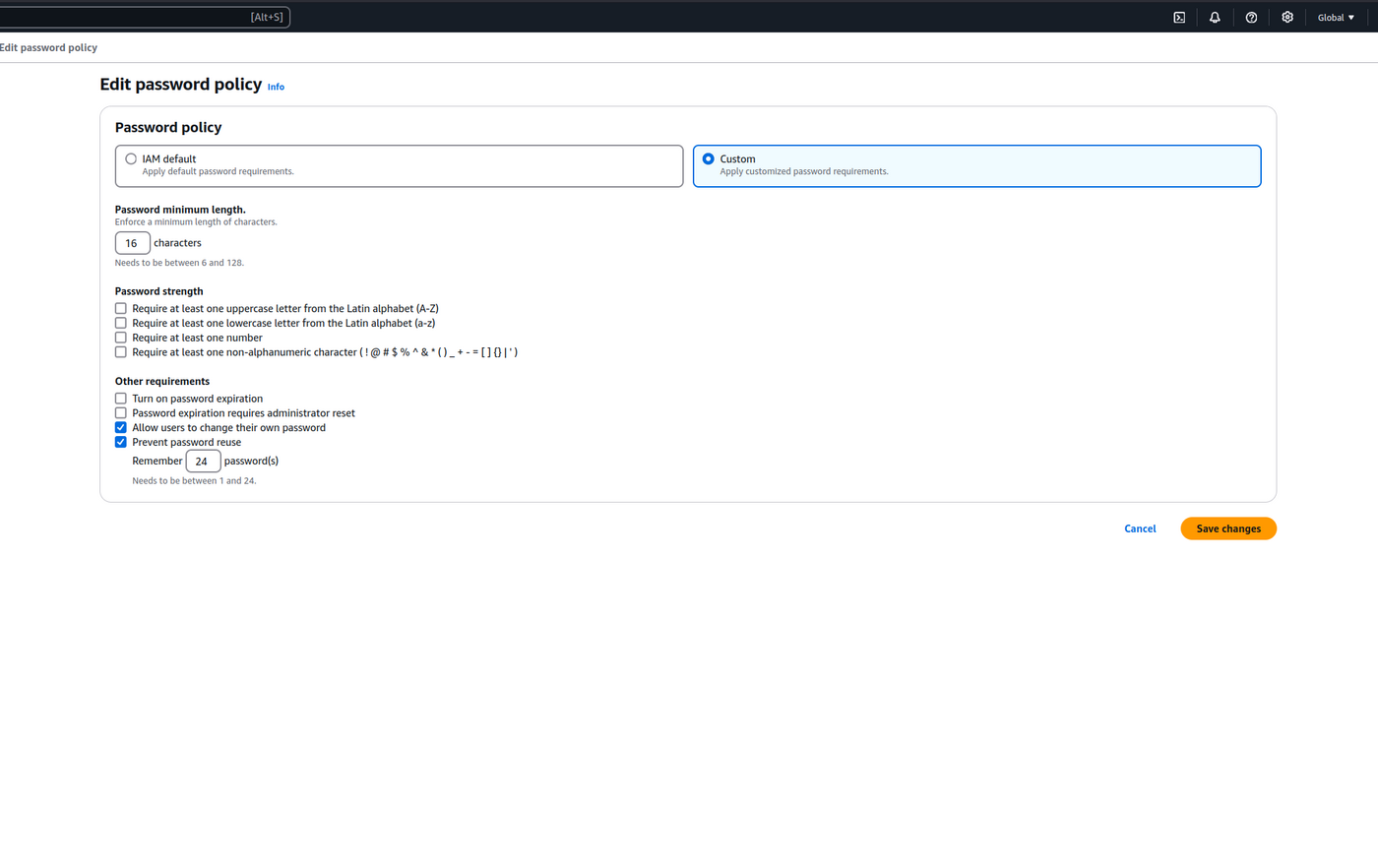
The AWS Password Policy dictates the security standards and management of AWS IAM User passwords used for access to the AWS Console. We extend the default policy to increase security and minimise additional processes providing the most efficient password management configuration we can design.
cspm cloud guidance